The Vault Protocol: Integrating Biometric Security into High-Net-Worth Collections
The safeguarding of a wine collection transcends mere physical security; it is an imperative born from the unique volatility of its contents and the significant capital appreciation inherent in aged vintages. This document delineates the strategic advantages of integrating advanced biometric access control systems within your wine cellar, transforming it from a repository into a fortified vault safeguarding your liquid assets. Our consultation focuses on the technical underpinnings of such an implementation, prioritizing the preservation of organoleptic integrity and the protection of irreplaceable vintages.
Unveiling the vulnerabilities of conventional cellar entry
Traditional cellar access mechanisms, often reliant on conventional keying systems or rudimentary electronic locks, present a demonstrable vulnerability in the context of a serious wine collection. These methods, while ostensibly securing a space, offer scant protection against determined unauthorized access or accidental compromise. The integrity of your collection, comprising years of diligent acquisition and significant capital investment, is thus predicated on a façade of security that can be easily breached. Consider the metaphorical parallel: a masterfully aged Bordeaux, meticulously cellared, is offered to a palate accustomed to the commonplace, its sublime nuances lost due to inadequate protection against dilution by the unsophisticated. Similarly, your collection, a testament to connoisseurship, is exposed when its guardian is easily bypassed.
The latent risk of key duplication and loss
The ubiquity of duplicated keys, whether through oversight or malicious intent, represents a fundamental flaw in traditional access protocols. A misplaced key, a compromised copy, or even the casual loan of a master key to an unqualified individual can initiate an irreversible cascade of security breaches. The potential for unauthorized removal of bottles, particularly those of high value, is a tangible threat. Furthermore, the very act of key management introduces an administrative burden that is often underestimated, diverting valuable time and resources from the core objective: preserving the cellar’s sanctity.
The limitations of mechanical and basic electronic locking systems
Mechanical locks, while offering a physical impediment, are susceptible to manipulation and brute force. Their efficacy diminishes with time and exposure to environmental factors within a cellar, such as humidity and temperature fluctuations, which can affect the precision of their mechanisms. Basic electronic locks, while offering a degree of convenience, often rely on rudimentary encryption or readily decipherable access codes. These systems, lacking sophisticated audit trails and granular access permissions, offer a false sense of security. The “digital fingerprint” of access is often smudged, leaving no definitive record of who entered, when, and under what circumstances.
The Dawn of Biometric Authentication: Fortifying the Threshold
Deconstructing the technical architecture of biometric access control

Biometric access control systems represent a paradigm shift in cellar security, moving beyond surrogate identifiers like keys and codes to immutable, inherent human characteristics. This technology leverages the uniqueness of individual biological traits to grant or deny entry, establishing a robust and auditable chain of access. The underlying principle is analogous to a highly discriminating palate, capable of discerning the subtle complexities of a rare varietal from a mass-produced imitation. By verifying the authentic “vintage” of the individual seeking entry, these systems elevate your cellar’s security to an unprecedented level.
Understanding the modalities: fingerprint, retinal, and facial recognition
The prevailing biometric modalities offer distinct advantages, each contributing to a multi-layered security architecture.
Fingerprint scanning: The fundamental identifier
Fingerprint recognition systems operate by capturing the unique ridge patterns on an individual’s fingertip. Advanced optical or capacitive sensors analyze these patterns, comparing them against a pre-enrolled database. The technical efficacy relies on algorithms that analyze minutiae points – the endings and bifurcations of ridges – ensuring a high degree of accuracy. The inherent advantage lies in the practicality and widespread familiarity of fingerprints as identifiers.
Retinal scanning: A deep biological signature
Retinal scanning technology analyzes the intricate vascular patterns within the retina at the back of the eye. This modality offers an exceptionally high level of uniqueness and stability, as retinal patterns are established early in life and remain unchanged. The process involves projecting a low-intensity infrared light onto the retina, capturing the absorption patterns of the blood vessels. The technical robustness of retinal scanning makes it exceedingly difficult to spoof.
Facial recognition: The dynamic yet distinctive matrix
Facial recognition systems map and analyze unique facial features, such as the distance between the eyes, the shape of the nose, and the contour of the jawline. Advanced algorithms create a unique facial template. While facial expressions can vary, sophisticated systems utilize 3D imaging and nodal point analysis to account for these changes, ensuring accurate identification over time. This modality offers a contactless and intuitive user experience, akin to recognizing a distinguished patron across a crowded salon.
The scientific foundation: Algorithms, templates, and matching
The core of any biometric system lies in its sophisticated algorithms. These algorithms process raw biometric data into a unique digital template – a mathematical representation of the captured characteristic. This template is not a direct image but a series of data points. Upon attempted access, a new template is generated from the presented biometric and compared against the enrolled templates in the system’s database. The matching process, often employing probabilistic scoring, determines the level of confidence in the identification. The accuracy of these algorithms is paramount, minimizing false positives (unauthorized access granted) and false negatives (authorized access denied). This precision is critical for maintaining the organoleptic integrity of your collection by preventing unauthorized access and ensuring that only those with legitimate access can interact with your liquid assets.
Integrating Biometrics: A Technical Blueprint for Preservation

Designing the seamless and secure entry point
The integration of a biometric access control system should not be an afterthought but a fundamental component of your cellar’s design. This approach ensures aesthetic harmony while maximizing functional efficacy, transforming the entryway into an architectural focal point that speaks of both sophistication and unwavering security. The hardware itself becomes an extension of the preservation technology, a sentinel guarding against the ephemeral threats that can compromise your collection.
The hardware: Selection and strategic placement
The selection of biometric hardware must be guided by the specific environmental conditions of your wine cellar. Factors such as temperature, humidity, and potential for dust ingress necessitate robust, industrial-grade sensors. Consider the lineage of a fine Champagne; its packaging is as crucial to its preservation as the méthode traditionnelle itself. Similarly, the hardware chosen for your biometric access system must be intrinsically resilient. Strategic placement is equally vital. The scanner, whether for fingerprint, iris, or facial recognition, should be positioned at an optimal height and angle to facilitate quick and accurate capture, ensuring a frictionless yet secure entry for authorized personnel. The placement should not disrupt the visual flow of the cellar’s aesthetic but rather enhance it, becoming a subtle emblem of advanced security.
The software: Management, user profiles, and audit trails
The intelligence of the system resides in its software. A robust platform will offer granular control over user profiles, allowing for the assignment of specific access privileges based on individual roles and responsibilities. This is akin to a vintner understanding the precise aging requirements for each varietal; not all wines require the same maturation period, and not all individuals require the same level of access. Furthermore, a comprehensive audit trail is indispensable. Every access attempt, whether successful or denied, should be meticulously logged, creating an unalterable record. This data provides invaluable insights into the security posture of your cellar, allowing for proactive identification of anomalies and ensuring accountability.
Power backup and environmental resilience: Ensuring continuous protection
Understanding the critical nature of your collection, any biometric system must incorporate redundant power solutions. Uninterruptible Power Supplies (UPS) and backup generators are essential to ensure continuous operation during power outages, preventing any lapse in security that could be exploited. Furthermore, the hardware and associated infrastructure must be designed to withstand the unique environmental conditions of a wine cellar, including stable temperature and humidity levels, and protection against potential water ingress. The resilience of the system mirrors the careful calibration of temperature and humidity required to protect the delicate balance of a maturing wine.
Beyond Access: Enhanced Security Protocols and Risk Mitigation
The symbiotic relationship between biometrics and environmental monitoring
The integration of biometric access control is not an isolated security measure but a critical element within a holistic approach to cellar management. Its efficacy is amplified when linked with advanced environmental monitoring systems, creating a truly fortified environment for your liquid assets. Imagine a symphony where each instrument plays its part in harmony; the biometric system is the conductor, ensuring authorized presence, while environmental sensors are the violins and cellos, maintaining the perfect pitch for preservation.
Real-time environmental anomaly detection and alerts
Biometric systems can be programmed to trigger specific responses in the event of detected environmental anomalies. For example, a sudden spike in temperature or humidity could automatically lock down access to unauthorized personnel and alert designated custodians. This proactive approach ensures that any deviation from optimal storage conditions is addressed with the utmost urgency, preventing potential damage to sensitive vintages. The system acts not merely as a gatekeeper but as an intelligent guardian, preempting threats before they can manifest.
Granular access for curated collection management
The ability to assign specific access levels extends beyond mere entry. It allows for curated management of your collection. For instance, a sommelier might have access to specific tiers of your cellar for tasting and inventory, while a conservator might have access for maintenance and assessment. This level of granular control minimizes the risk of accidental damage or misplacement of bottles, ensuring that each vintage is handled by individuals with the requisite expertise and authorization. This meticulous approach mirrors the intricate process of decanting a rare and delicate wine, where trained hands ensure its perfect presentation.
The extended arm of security: remote monitoring and management
Modern biometric systems often integrate with remote monitoring platforms. This allows authorized individuals to oversee cellar access and environmental conditions from any location, providing an unparalleled level of oversight. This capability is crucial for collectors who travel frequently or who manage multiple cellar locations. The system becomes an extension of your presence, a silent sentinel ensuring the perpetual security of your liquid assets, regardless of your physical proximity.
The Walnut Creek Imperative: A Consultation of Distinction
Experiencing the future of wine preservation firsthand
The safeguarding of a significant wine collection is a profound responsibility, demanding a commitment to the highest standards of preservation technology and access control. Our approach at Walnut Creek is grounded in a deep understanding of both the scientific principles underpinning wine aging and the sophisticated technological solutions available to protect your investments. We do not merely offer hardware; we provide a comprehensive strategy for the unwavering security and optimal aging of your liquid assets.
A showroom experience dedicated to the discerning collector
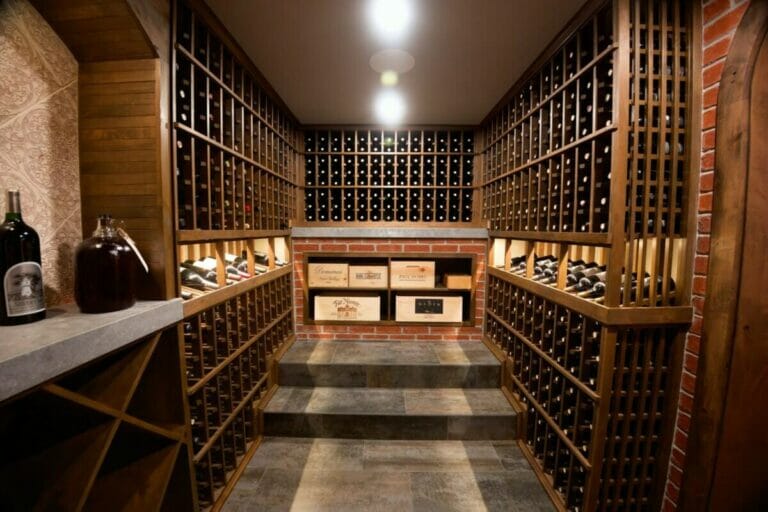
The Walnut Creek showroom is not merely a retail space; it is an immersive experience designed for the discerning collector. Here, you will witness firsthand the elegant integration of advanced biometric access control systems within simulated cellar environments. Our team of specialists, conversant in both horology and viticulture, will guide you through the technical intricacies of each system, demonstrating how these sophisticated technologies contribute to the organoleptic integrity and capital preservation of your wine. This is an opportunity to understand the “why” behind the “what,” to appreciate the technical prowess that underpins the aesthetic beauty of our solutions.
Engaging the expertise for your bespoke cellar strategy
We invite you to schedule a private consultation at our Walnut Creek showroom. This is an opportunity to engage directly with our senior brand strategists and technical advisors. We will discuss your specific collection needs, environmental considerations, and security objectives. By understanding your unique requirements, we can then collaboratively design a bespoke cellar access control strategy that elevates the security of your liquid assets to the level they deserve, transforming your cellar into a technologically advanced sanctuary, a true vault for your liquid legacy. This is not an offer to purchase, but an invitation to engage in a rigorous consultation, to explore the possibilities of uncompromising security and preservation.
FAQs
What is biometric cellar access control?
Biometric cellar access control is a security system that uses unique biological characteristics, such as fingerprints, facial recognition, or iris scans, to grant authorized individuals access to a cellar or storage area.
How does biometric access improve cellar security?
Biometric access enhances security by ensuring that only registered users with verified biometric data can enter the cellar, reducing the risk of unauthorized access compared to traditional key or code-based systems.
What types of biometric technologies are commonly used for cellar access?
Common biometric technologies for cellar access include fingerprint scanners, facial recognition cameras, and iris or retina scanners, each providing a different method of verifying a person’s identity.
Is biometric cellar access control difficult to install?
Installation complexity varies depending on the system chosen, but many biometric access control devices are designed for straightforward integration with existing door locks and security systems, often requiring professional installation for optimal performance.
Can biometric cellar access control systems be integrated with other security measures?
Yes, biometric cellar access control systems can often be integrated with alarms, surveillance cameras, and remote monitoring systems to provide a comprehensive security solution for cellars and storage areas.